RESOURCES
What is TEMPEST?
The TEMPEST specification (designated by US National Security Agency) refers to the susceptibility of computer and telecommunications devices to data theft. Some electronic equipment emits electromagnetic radiation or compromising emanations (CE) in a manner that can be used to reconstruct intelligible data. The NSA identifies this as a concern in situations where classified information may be accessible and must be protected from outside agents. For any system, there are specific frequencies of interest that must be suppressed to keep the information undecipherable.
Protecting equipment from espionage is accomplished through distance, shielding, filtering, and masking. The TEMPEST standards mandate elements such as equipment distance from walls, amount of shielding in buildings, and equipment. It also mandates the distance separating wires carrying classified vs. unclassified materials, filters on cables, and even distance and shielding between the equipment and building pipes.
Sources of Compromising Emanation TEMPEST Signals:
The sources of compromising emanations (CE) may include any electromechanical and/or electronic equipment used to process secure information. The generation of some types of CE has increased due to a trend toward compactness, forcing conductors, components, and circuits into closer proximity. This often makes coupling between secure and nonsecure elements unavoidable. The signals do not need to be of great magnitude to be compromising because intercepting receiving instruments can make use of very small amounts of energy.
There are two basic sources of such signals:
- Functional Sources - Functional sources are designed for the specific purpose of generating electromagnetic energy. Examples include switching transistors, oscillators, and signal generators.
- Incidental Sources - Incidental sources are those which are not designed for the specific purpose of generating electromagnetic energy but do so unintentionally. Examples include electromechanical switches, brush motors, etc.
Types of TEMPEST Signals:
The most common types of Compromising Emanations are:
- RED Baseband Signals - RED baseband signal is a type of CE that can be introduced into electrical conductors connected to circuits within equipment.
- Modulated Spurious Carriers - This type of CE is generated as the modulation of a carrier by RED data. As an example, the carrier can be the switching frequency of a power supply. The carrier is usually amplitude or angle-modulated by the basic RED data signal or a signal related to the basic RED data signal.
- Impulsive Emanations - Impulsive emanations are caused by very fast transitions of digital signals.
Note: RED telecommunication systems include all equipment, wirelines, components, and systems that process National Security Information (NSI). BLACK telecommunication systems includes all equipment, wirelines, components, and systems that process encrypted or non-NSI data. BLACK lines and other electrically conductive materials that enter the secure RED space are potential carriers of Compromising Emanations via inadvertent coupling with RED lines. RED/BLACK telecommunication systems are discussed further in the following section.
.jpg?width=516&name=Propagation%20of%20tempest%20signals_%20(1).jpg)
Propagation of TEMPEST Signals
There are four basic means by which compromising emanations may be propagated. These are:
- Electromagnetic Radiation - This electromagnetic field generated by RED signals can be either detected outside the Secure Space or coupled onto BLACK lines connected to or located near, the equipment that exit the secure space.
- Line Conduction – In this case, CE is conducted as signal/noise on the external or interface lines. The external lines include signal lines, control and indicator lines, and AC and DC powerlines, nonelectric wires/cables, conduits, ducts, etc.
- Modulation of an intended signal – Here, the carrier is an intended signal being transmitted. However, it is amplified or angle-modulated by the basic RED data signal or a signal related to the basic RED data signal. It is then radiated into space or coupled into the equipment’s external conductors.
- Acoustics – Other sources of CE exist where mechanical operations occur, and sound is produced. Keyboards, printers, relays - these produce sound and consequently can be sources of compromise.
RED/BLACK Telecommunication Systems
Standard RED/BLACK handling criteria define physical separation guidelines to decrease the probability that electromagnetic emissions from RED devices might couple to BLACK systems.
- The RED/BLACK concept is the basis for the development of secure facility criteria, discussed in detail throughout our TEMPEST blog series. The RED/BLACK concept dictates that electrical and electronic circuits, components, equipment, systems, etc., which handle national security plain language information in an electrical signal form (RED) be separated from those handling encrypted or unclassified information (BLACK).
- RED/BLACK guidelines have been developed to detail the procedures required for proper equipment and system shielding, separation, grounding, and filtering to minimize TEMPEST signals.
Equipment Design:
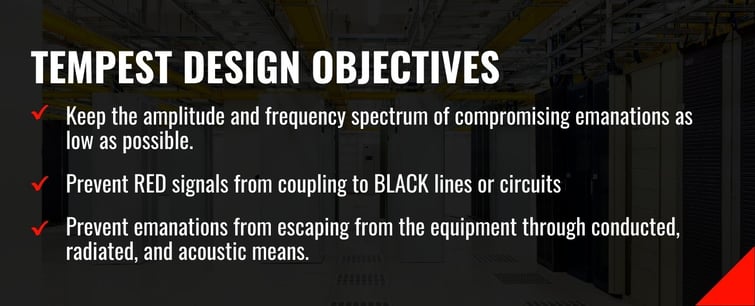
TEMPEST security issues are best prevented by meticulous design consideration at each stage of the equipment or system development. Although it is nearly impossible to completely prevent the generation of such compromising emanations, the following objectives guide best practice for TEMPEST system design:
- Minimize amplitude and frequency spectrum for all compromising emanations
- Prevent RED signals from coupling to BLACK lines or circuits
- Prevent emanations from escaping from the equipment through conducted, radiated, and acoustic means
Consideration for TEMPEST Equipment/Facility Design
When designing a Tempest equipment/facility or retrofitting commercial equipment, some or all the following techniques can be helpful:
- Preventive Measures - Identify RED signals and circuits. This identification serves as a basis for all preventive/containment methods which may follow.
- Functions and Format Selections - RED data handling schemes or input/output techniques.
- Signal Power Levels - The signal operating levels of all RED data circuits and stages should be as low as possible to minimize propagation of compromising emanations.
- Signal Spectrum Limits - The objective is to limit the spectra of RED data signals to contain their energies within the RED environment.
- Circuit Arrangement and Layout - Prevention of coupling RED signal processing circuits onto BLACK circuits by separating those to minimizing interelement and inter-circuit RED signal paths.
- Return Path Layout – Excessive return path lengths and impedances between various points of the return paths for power and signal currents can result in unintentional inter-circuit signal coupling and spurious signal generation. Common return paths for RED and BLACK return currents must be avoided.
- Stage Decoupling - Without adequate decoupling, currents and voltages representing compromising emanations can be propagated from an originating element through the equipment power supply via power leads.
- Shielding - Shielding separates two regions so that, in passing from one to the other, an electric/ magnetic field is attenuated by reflection and absorption losses. Shielding can be accomplished with conductor and/or cable shields, conduit, gaskets, magnetic foils, screens, and shielded enclosures.
- Filtering - A filter functions by allowing certain frequencies to pass while attenuating all others. The filters used for compromising emanation containment usually are low-pass interference reduction types. They are used on signal lines (analog or digital), control lines, and powerlines. To perform effectively, they must be selected with care to ensure correct pass and stop bands, attenuation levels, and input-output impedance. In some instances, special designs are required. The filters must be located and installed at the point of power/control/signal entry and exit to the RED equipment / secure shielded compartment (SCIF). Adherence to established installation guidelines and is critical. High input-output isolation for both conducted and radiated signals must be created.
- Isolation – Circuit isolation is achieved through the use of transformers, feedback amplifiers, or optical couplers. In some applications, these can be more effective than an EMI filter.

Frequently Asked Questions About TEMPTEST
Partner with Astrodyne TDI
Astrodyne TDI is an industry leader in the design and manufacturing of EMI Filters for a variety of applications including TEMPEST systems. With over 60 years in the power industry, a staff of highly experienced professionals, and a global reach, we specialize in creating valuable solutions to meet our client's unique needs. Our team can help you select the best EMI filter and power solution and guide you through the design or retrofit process to ensure full compliance with TEMPEST requirements. Contact Astrodyne TDI today to learn more about how we can assist you with your TEMPEST needs.



